Miscellaneous Questions
Here you will find answers to Miscellaneous Questions
Question 1
Which statement accurately describes one difference between a small office and medium office topology?
A. Small offices commonly use Rapid PVST+ for Layer 3 deployments.
B. Medium offices commonly use integrated route and switching platforms.
C. Medium offices use integrated 10/100/1000 interfaces as Layer 2 trunks.
D. Medium offices use external access switches to support LAN connectivity.
Answer: D
Question 2
Which statement can a network designer use to describe route summarization to an IT manager?
A. It is the grouping of multiple contiguous subnets into one Class A, B, or C IP address to minimize routing table size.
B. It is the grouping of multiple discontiguous subnets to increase routing performance.
C. It is the grouping of multiple contiguous networks and advertising as one large network.
D. It is the grouping of ISP network addresses to minimize the number of routes to the Internet.
Answer: C
Question 3
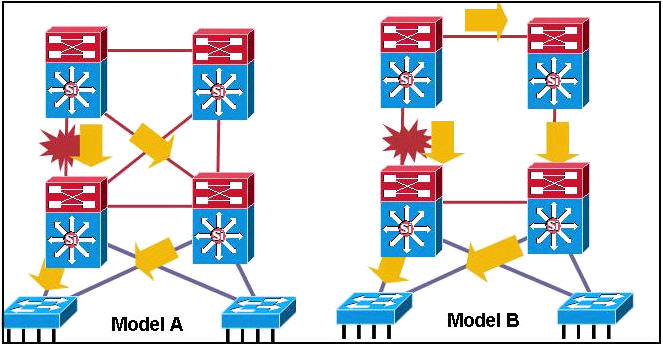
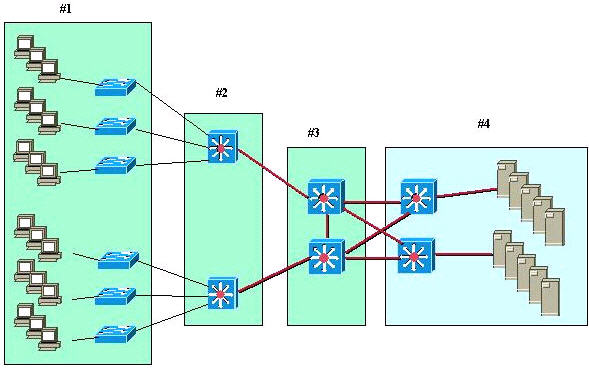
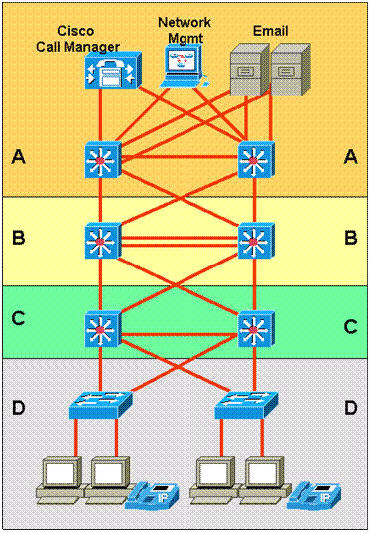
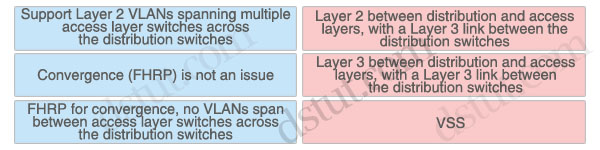
Refer to the exhibit.
Which two statements describe why Model A is the recommended design
for routing between Building Distribution switches and Campus Core
switches? (Choose two)
A. It uses timer-based non-deterministic convergence.
B. It is software-based, providing fast convergence to the remaining path.
C. Routes are not summarized from distribution to the core.
D. The Layer 3 redundant equal cost links support fast convergence.
E. A link or box failure does not require routing protocol convergence.
Answer: D E
Question 4
RST Corporation is planning to upgrade its current network. The chief
technology officer has supplied a topology diagram and an IP addressing
scheme of the current network during an interview. RST has been growing
at about twenty percent per year. It has been difficult to maintain
customer support at a satisfactory level. Therefore, the RST board has
met with and directed the chief technology officer to look into network
improvements. Which two items are most relevant in documenting RST’s
business requirements? (Choose two)
A. projected growth estimates
B. network performance requirements
C. existing network topologies
D. improved customer support requirements
E. the IP addresses assigned by the ISP
Answer: A D
Question 5
You are designing a small branch office that requires these attributes:
support for 60 users
the growth capacity to add another 15 users soon
redundant access higher bandwidth between the Layer 2 switch and routing to the WAN
Which branch office topology or technology must be used?
A. two-tier
B. loop-free
C. three-tier
D. EtherChannel
E. integrated routing and switching
Answer: D
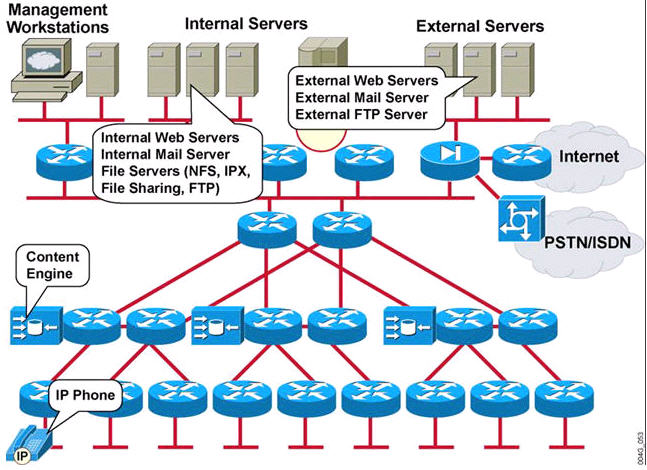
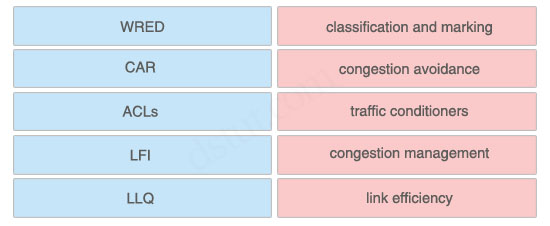
Question 6
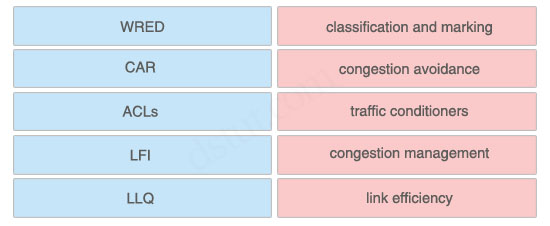
A campus network needs end-to-end QoS tools to manage traffic and
ensure voice quality. Which three types of QoS tools are needed? (Choose
three)
A. interface queuing and scheduling
B. congestion management
C. compression and fragmentation
D. bandwidth provisioning
E. traffic classification
F. buffer management
Answer: A D E
Question 7
After a period of rapid growth, FloCzar Boats is seeking better network management tools.
Managers have developed this needs list:
Move from static to dynamic device information.
Gain information to assist in long-term trend analysis.
Concentrate on Layer 4 monitoring.
Which management protocol will most help FloCzar achieve its goals?
A. Cisco Discovery Protocol
B. RMON
C. SNMP
D. RMON2
E. NetFlow
Answer: D
Question 8
A network design document is being prepared for a customer. Which three network design elements must be included? (Choose three)
A. data sources
B. design details
C. proof of concept
D. implementation plan
E. organizational policies
Answer: B C D
Question 9
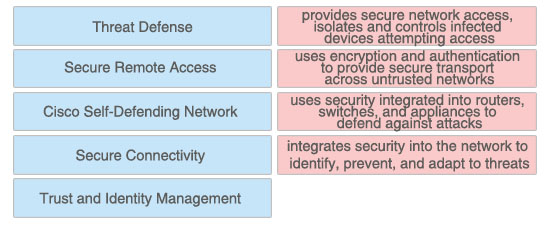
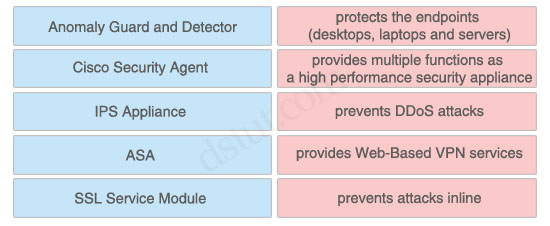
A company is implementing an Identity Management solution with these characteristics:
existing Cisco ACS 4.0
Cisco Catalyst switches
minimal added investments
Which Cisco Trust and Identity solution would you recommend?
A. NAC Appliance (Cisco Clean Access)
B. Cisco IBNS
C. NAC Framework
D. Cisco Security Agent
E. CSM
F. Cisco Security MARS
Answer: B
Question 10
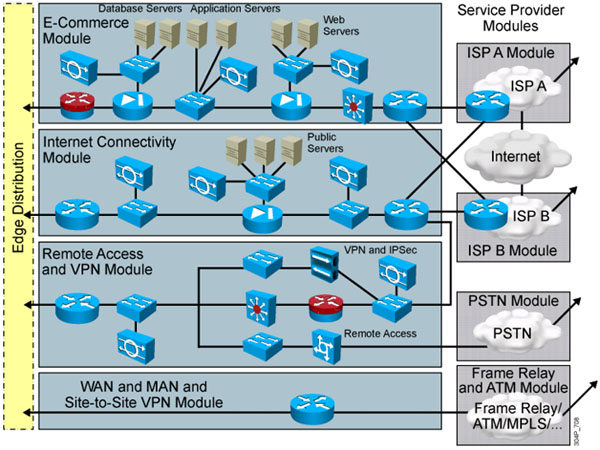
The BodMech online fitness organization specializes in creating
fitness plans for senior citizens. The company recently added a
health-products retail inventory. Which E-Commerce module device will
allow customers to interact with the company and purchase products?
A. application server
B. database server
C. public server
D. web server
E. NIDS appliance
F. SMTP mail server
Answer: D
Question 11
A network design includes private addressing, but there is also a
need for two or three network devices to each be assigned a unique
public address so they can be accessed from the Internet. Which
technique will satisfy this requirement?
A. Dynamic NAT
B. Static NAT
C. DHCP
D. VPN tunneling
Answer: B
Question 12
In a Cisco CatOS switch, what is the recommended practice when
configuring switch-to-switch intercommunications to carry multiple VLANs
for Dynamic Trunk Protocol?
A. auto to auto_negotiate
B. auto to auto_no_negotiate
C. on to on_negotiate
D. desirable to desirable_negotiate
E. desirable to desirable_no_negotiate
F. disable Dynamic Trunk Protocol when operating in the distribution layer
Answer: D
Question 13
The topology map in the draft design document should cover which two layers of the OSI model? (Choose two)
A. physical
B. data link
C. network
D. transport
E. session
F. application
Answer: A C
Question 14
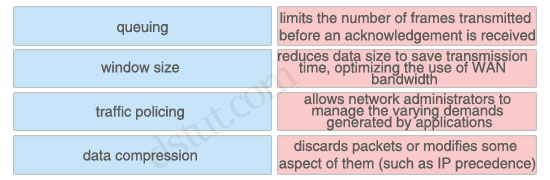
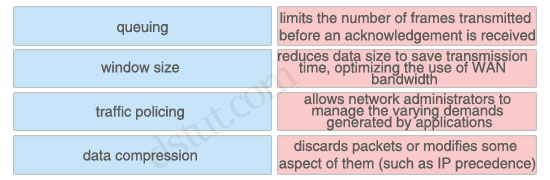
Which statement correctly describes queuing in environments supporting teleworkers?
A. CQ is for time-sensitive protocols.
B. Queuing occurs on the outbound interface.
C. Priority queuing guarantees some level of sen/ice to all traffic.
D. Hardware queues are configured for appropriate PQ, CQ, or WFQ.
E. WFQ is the Cisco IOS default on all WAN links regardless of speed.
Answer: B
Question 15
Which two methods are used to enhance VPN performance on Cisco ISRs? (Choose two)
A. built-in hardware-based encryption acceleration
B. SSL Acceleration Network Module
C. high-performance VPN encryption AIM
D. VPN Service Adapter
E. VPN Acceleration Module
F. VPN Shared Port Adapter
Answer: A C
Question 16
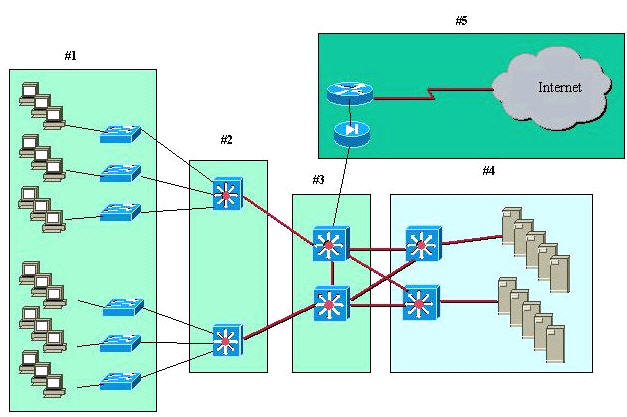
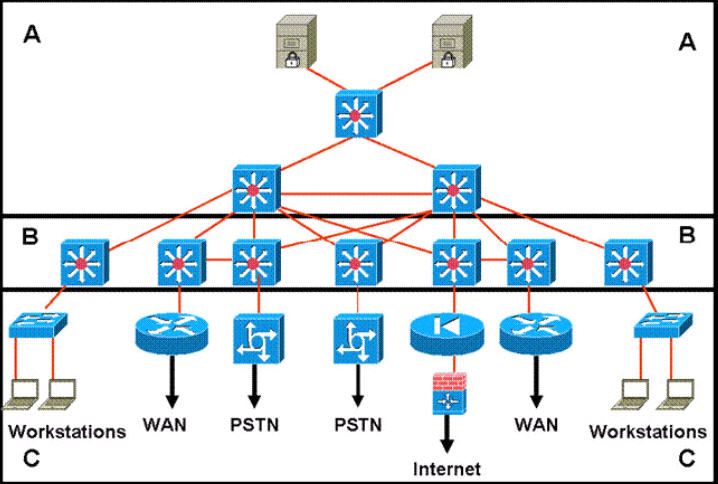
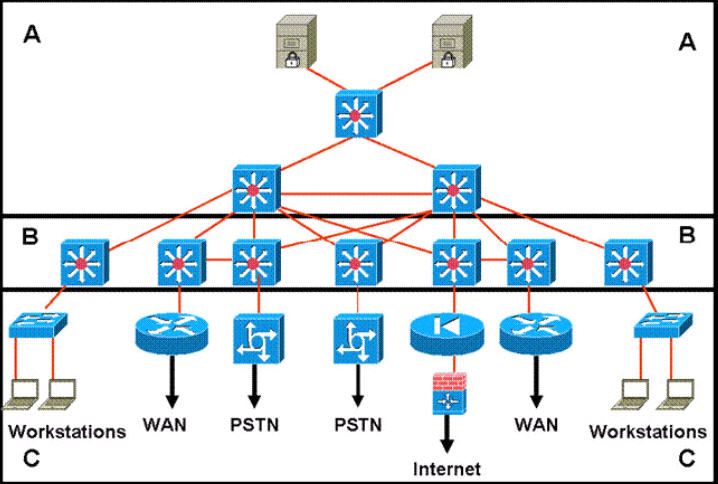
Refer to the exhibit.
A standard Layer 2 campus network design is pictured. Which numbered box represents the core layer?
A. #1
B. #2
C. #3
D. #4
E. #5
Answer: C
Question 17
What is the recommended spanning tree protocol to use for all Layer 2 deployments in a branch office environment?
A. CST
B. RSPT
C. PVST
D. MISTP
E. Rapid PVST+VP
Answer: E
Question 18
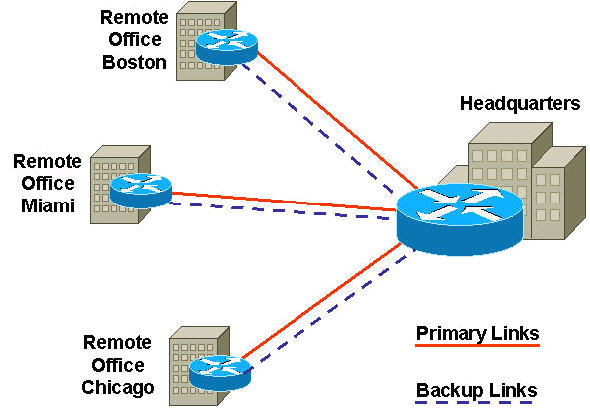
Which two of these are scalability benefits of designing a network that utilizes VPNs?(Choose two)
A. extends the network to remote users
B. allows networks to be set up and restructured quickly
C. reduces dial infrastructure expenditures
D. reduces the number of physical connections
E. simplifies the underlying structure of a customer WAN
Answer: D E
Question 19
Which two capabilities of NetFlow accounting assist designers with network planning?(Choose two)
A. the decoding and analyzing of packets
B. the monitoring of processor time on network devices
C. the monitoring of user network utilization
D. the calculation of packet and byte counts of network traffic
E. the presentation of a time-based view of application usage on the network
Answer: C D
Question 20
Refer to the exhibit.
435 Cisco model 2800 routers
129 Cisco model 3800 routers
10 Cisco model 7500 routers |
You are documenting the existing network of a customer with a large
installed Cisco network. The routers listed are in use on the network.
Which two additional pieces of information would be the most valuable in
completing your documentation of these routers? (Choose two)
A. error statistics
B. interface options
C. software revisions
D. power requirements
E. management protocols
Answer: B C
Question 21
Which two design criteria require VLANs in a proposed solution? (Choose two)
A. video streaming on the LAN
B. security between departments
C. the segmenting of collision domains
D. the segmenting of broadcast domains
E. the use of multivendor equipment
F. a limited corporate budget
Answer: B D