Here you will find answers to Drag and Drop Questions – Part 1
Question 1
Drag the data center property on the left to the design aspect on the right it is most apt to affect
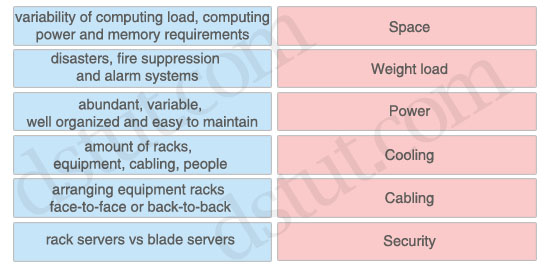
Answer:
Space: amount of racks, equipment, cabling, people
Weight load: rack servers vs blade servers
Power: variability of computing load, computing power and memory requirements
Cooling: arranging equipment racks face-to-face or back-to-back
Cabling: abundant, variable, well organized and easy to maintain
Security: disasters, fire suppression and alarm systems
Weight load: rack servers vs blade servers
Power: variability of computing load, computing power and memory requirements
Cooling: arranging equipment racks face-to-face or back-to-back
Cabling: abundant, variable, well organized and easy to maintain
Security: disasters, fire suppression and alarm systems
Explanation
The data center space includes number of racks for equipment that will be installed. Other factor needs to be considered is the number of employees who will work in that data center.
Rack servers are low cost and provide high performance, unfortunately they take up space and consume a lot of energy to operate. Blade servers provide similar computing power when compared to rack mount servers, but require less space, power, and cabling. The chassis in most blade servers allows for shared power, Ethernet LAN, and Fibre Channel SAN connections, which reduce the number of cables needed.
The power in the data center facility is used to power cooling devices, servers, storage equipment, the network, and some lighting equipment. In server environments, the power usage depends on the computing load place on the server. For example, if the server needs to work harder by processing more data, it has to draw more AC power from the power supply, which in turn creates more heat that needs to be cooled down.
Cooling is used to control the temperature and humidity of the devices. The cabinets and racks should be arranged in the data center with an alternating pattern of “cold” and “hot” aisles. The cold aisle should have equipment arranged face to face, and the hot aisle should have equipment arranged back to back. In the cold aisle, there should be perforated floor tiles drawing cold air from the floor into the face of the equipment. This cold air passes through the equipment and flushes out the back into the hot aisle. The hot aisle does not have any perforated tiles, and this design prevents the hot air from mixing with the cold air.
The cabling in the data center is known as the passive infrastructure. Data center teams rely on a structured and well-organized cabling plant. It is important for cabling to be easy to maintain, abundant and capable of supporting various media types and requirements for proper data center operations.
Fire suppression and alarm systems are considered physical security and should be in place to protect equipment and data from natural disasters and theft.
(Reference: CCDA 640-864 Official Cert Guide)
Question 2
Drag the WAN characteristic on the left to the branch office model where it would most likely be used on the right
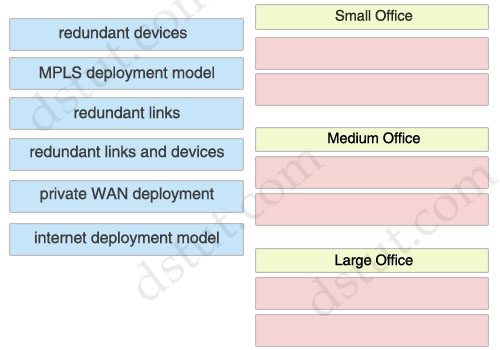
Answer:
Small Office:
+ redundant links
+ internet deployment model
+ redundant links
+ internet deployment model
Medium Office:
+ redundant devices
+ private WAN deployment
+ redundant devices
+ private WAN deployment
Large Office:
+ MPLS deployment model
+ redundant links and devices
+ MPLS deployment model
+ redundant links and devices
Explanation
Small Office:
The small office is recommended for offices that have up to 50 users. The Layer 3 WAN services are based on the WAN and Internet deployment model. A T1 is used for the primary link, and an ADSL secondary link is used for backup.
Medium Office:
The medium branch design is recommended for branch offices of 50 to 100 users. Medium Offices often use redundancy gateway services like Hot Standby Router Protocol (HSRP) or Gateway Load Balancing Protocol (GLBP).
Private WAN generally consists of Frame Relay, ATM, private lines, and other traditional WAN connections. If security is needed, private WAN connections can be used in conjunction with encryption protocols such as Digital Encryption Standard (DES), Triple DES (3DES), and Advanced Encryption Standard (AES). This technology is best suited for an enterprise with moderate growth outlook where some remote or branch offices will need to be connected in the future.
Dual Frame Relay links in medium office provide the private WAN services, which are used to connect back to the corporate offices via both of the access routers.
Large Office:
The large office supports between 100 and 1000 users. The WAN services use an MPLS deployment model with dual WAN links into the WAN cloud -> MPLS & redundant links.
(Reference: CCDA 640-864 Official Cert Guide)
Question 3
Drag the security provision on the left to the appropriate network module on the right
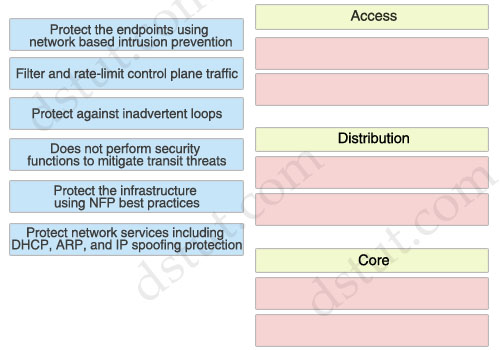
Answer:
Access:
+ Protect network services including DHCP, ARP, and IP spoofing protection
+ Protect against inadvertent loops
+ Protect network services including DHCP, ARP, and IP spoofing protection
+ Protect against inadvertent loops
Distribution:
+ Protect the endpoints using network based intrusion prevention
+ Protect the infrastructure using NFP best practices
+ Protect the endpoints using network based intrusion prevention
+ Protect the infrastructure using NFP best practices
Core:
+ Does not perform security functions to mitigate transit threats
+ Filter and rate-limit control plane traffic
+ Does not perform security functions to mitigate transit threats
+ Filter and rate-limit control plane traffic
Explanation
Rate limiting controls the rate of bandwidth that incoming traffic is using, such as ARPs and DHCP requests.
Access layer:
Some security measures used for securing the campus access layer, including the following:
* Securing the endpoints using endpoint security software
* Securing the access infrastructure and protecting network services including DHCP, ARP, IP spoofing protection and protecting against inadvertent loops using Network Foundation Protection (NFP) best practices and Catalyst Integrated Security Features (CISF).
* Securing the endpoints using endpoint security software
* Securing the access infrastructure and protecting network services including DHCP, ARP, IP spoofing protection and protecting against inadvertent loops using Network Foundation Protection (NFP) best practices and Catalyst Integrated Security Features (CISF).
Distribution layer:
Security measures used for securing the campus distribution layer including the following:
* Protecting the endpoints using network-based intrusion prevention
* Protection the infrastructure using NFP best practices
* Protecting the endpoints using network-based intrusion prevention
* Protection the infrastructure using NFP best practices
Core layer:
The primary role of security in the enterprise core module is to protect the core itself, not to apply policy to mitigate transit threats traversing through the core.
The following are the key areas of the Network Foundation Protection (NFP) baseline security best practices applicable to securing the enterprise core:
* Infrastructure device access—Implement dedicated management interfaces to the out-of-band (OOB) management network, limit the accessible ports and restrict the permitted communicators and the permitted methods of access, present legal notification, authenticate and authorize access using AAA, log and account for all access, and protect locally stored sensitive data (such as local passwords) from viewing and copying.
* Routing infrastructure—Authenticate routing neighbors, implement route filtering, use default passive interfaces, and log neighbor changes.
* Device resiliency and survivability—Disable unnecessary services, filter and rate-limit control-plane traffic, and implement redundancy.
* Network telemetry—Implement NTP to synchronize time to the same network clock; maintain device global and interface traffic statistics; maintain system status information (memory, CPU, and process); and log and collect system status, traffic statistics, and device access information.
(Reference: Above information is extracted from
+ http://www.cisco.com/en/US/docs/solutions/Enterprise/Security/SAFE_RG/chap5.html for Access & Distribution Layers
+ http://www.cisco.com/en/US/docs/solutions/Enterprise/Security/SAFE_RG/chap3.html for Core Layer)
+ http://www.cisco.com/en/US/docs/solutions/Enterprise/Security/SAFE_RG/chap3.html for Core Layer)
Question 4
Drag the Campus Layer Design on the left to the appropriate location on the right
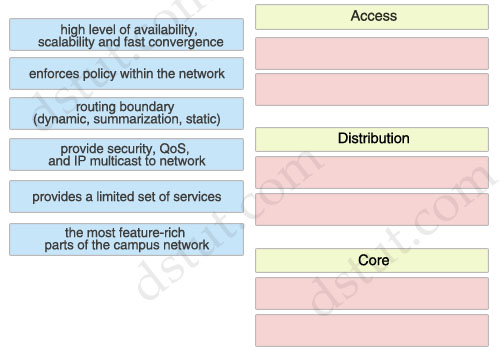
Answer:
Access:
+ routing boundary (dynamic, summarization, static)
+ the most feature-rich parts of the campus network
+ routing boundary (dynamic, summarization, static)
+ the most feature-rich parts of the campus network
Distribution:
+ enforces policy within the network
+ provide security, QoS, and IP multicast to network
+ enforces policy within the network
+ provide security, QoS, and IP multicast to network
Core:
+ high level of availability, scalability and fast convergence
+ provides a limited set of services
+ high level of availability, scalability and fast convergence
+ provides a limited set of services
Explanation
Campus Access Layer Network Design
The access layer is the first tier or edge of the campus, where end devices such as PCs, printers, cameras, Cisco TelePresence, etc. attach to the wired portion of the campus network. The wide variety of possible types of devices that can connect and the various services and dynamic configuration mechanisms that are necessary make the access layer one of the most feature-rich parts of the campus network.
Campus Distribution Layer
The campus distribution layer provides connectivity to the enterprise core for clients in the campus access layer. It aggregates the links from the access switches and serves as an integration point for campus security services such as IPS and network policy enforcement.
Distribution layer switches perform network foundation technologies such as routing, quality of service (QoS), and security.
Core Layer
The core layer provides scalability, high availability, and fast convergence to the network. The core layer is the backbone for campus connectivity, and is the aggregation point for the other layers and modules in the Cisco Enterprise Campus Architecture. The core provides a high level of redundancy and can adapt to changes quickly. Core devices are most reliable when they can accommodate failures by rerouting traffic and can respond quickly to changes in the network topology. The core devices implement scalable protocols and technologies, alternate paths, and load balancing. The core layer helps in scalability during future growth.
The campus core is in some ways the simplest yet most critical part of the campus. It provides a very limited set of services and is designed to be highly available and operate in an “always-on” mode. In the modern business world, the core of the network must operate as a non-stop 7x24x365 service.
Note:
It is a difficult question! Some characteristics are present at more than one layer so it is difficult to classify correctly. For example, a Cisco site says:
“The campus distribution layer acts as a services and control boundary between the campus access layer and the enterprise core. It is an aggregation point for all of the access switches providing policy enforcement, access control, route and link aggregation, and the isolation demarcation point between the campus access layer and the rest of the network.”
It means that the “routing boundary” should belong to the Distribution Layer instead of Access Layer. But the Distribution Layer also “enforces policy within the network” & “provide security, QoS, and IP multicast to network”.
After a lot of research, I decide to put the “routing boundary” to the Access Layer because this feature seems to be at the border of Access & Distribution layers so we can choose either. The “provide security, QoS, and IP multicast to network” features mainly belong to the Distribution layer (the Official 640-864 CCDA mentions about QoS, Security filtering & Broadcast or multicast domain definition in the Distribution layer)
Reference:
Question 5
Drag the WAN technology on the left to the most appropriate category on the right
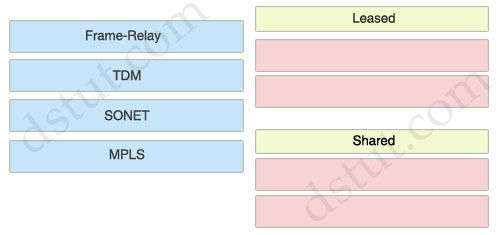
Answer:
Leased:
+ TDM
+ SONET
+ TDM
+ SONET
Shared:
+ Frame-Relay
+ MPLS
+ Frame-Relay
+ MPLS
Explanation
TDM & SONET are circuit-based so they are leased-line while Frame-Relay & MPLS are shared-circuit or packet-switched WAN
Question 6
Drag the technology on the left to the type of enterprise virtualization where it is most likely to be found on the right
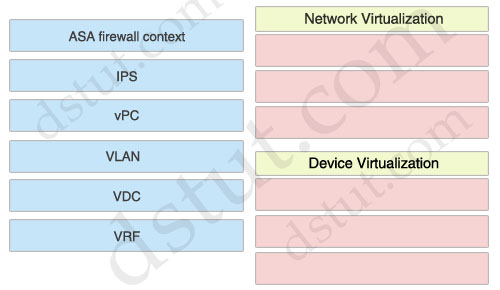
Answer:
Network Virtualization:
+ VLAN
+ vPC
+ VRF
+ VLAN
+ vPC
+ VRF
Device Virtualization:
+ ASA firewall context
+ IPS
+ VDC
+ ASA firewall context
+ IPS
+ VDC
Explanation
Network virtualization encompasses logical isolated network segments that share the same physical infrastructure. Each segment operates independently and is logically separate from the other segments. Each network segment appears with its own privacy, security, independent set of policies, QoS levels, and independent routing paths.
Here are some examples of network virtualization technologies:
* VLAN: Virtual local-area network
* VSAN: Virtual storage-area network
* VRF: Virtual routing and forwarding
* VPN: Virtual private network
* vPC: Virtual Port Channel
* VLAN: Virtual local-area network
* VSAN: Virtual storage-area network
* VRF: Virtual routing and forwarding
* VPN: Virtual private network
* vPC: Virtual Port Channel
Device virtualization allows for a single physical device to act like multiple copies of itself. Device virtualization enables many logical devices to run independently of each other on the same physical piece of hardware. The software creates virtual hardware that can function just like the physical network device. Another form of device virtualization entails using multiple physical devices to act as one logical unit.
Here are some examples of device virtualization technologies:
* Server virtualization: Virtual machines (VM)
* Cisco Application Control Engine (ACE) context
* Virtual Switching System (VSS)
* Cisco Adaptive Security Appliance (ASA) firewall context
* Virtual device contexts (VDC)
* Server virtualization: Virtual machines (VM)
* Cisco Application Control Engine (ACE) context
* Virtual Switching System (VSS)
* Cisco Adaptive Security Appliance (ASA) firewall context
* Virtual device contexts (VDC)
(Reference: CCDA 640-864 Official Cert Guide)
Question 7
Drag the network function on the left to the functional area or module where it is most likely to be performed in the enterprise campus infrastructure on the right
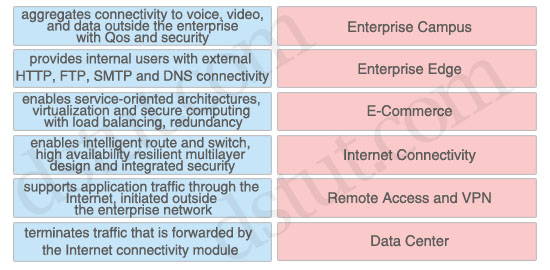
Answer:
Enterprise Campus: enables intelligent route and switch, high availability resilient multilayer design and integrated security
Enterprise Edge: aggregates connectivity to voice, video, and data outside the enterprise with Qos and security
E-Commerce: supports application traffic through the Internet, initiated outside the enterprise network
Internet Connectivity: provides internal users with external HTTP, FTP, SMTP and DNS connectivity
Remote Access and VPN: terminates traffic that is forwarded by the Internet connectivity module
Data Center: enables service-oriented architectures, virtualization and secure computing with load balancing, redundancy
Enterprise Edge: aggregates connectivity to voice, video, and data outside the enterprise with Qos and security
E-Commerce: supports application traffic through the Internet, initiated outside the enterprise network
Internet Connectivity: provides internal users with external HTTP, FTP, SMTP and DNS connectivity
Remote Access and VPN: terminates traffic that is forwarded by the Internet connectivity module
Data Center: enables service-oriented architectures, virtualization and secure computing with load balancing, redundancy
Access:
+ Protect network services including DHCP, ARP, and IP spoofing protection
+ Protect against inadvertent loops
+ Protect network services including DHCP, ARP, and IP spoofing protection
+ Protect against inadvertent loops
Distribution:
+ Protect the endpoints using network based intrusion prevention
+ Protect the infrastructure using NFP best practices
+ Protect the endpoints using network based intrusion prevention
+ Protect the infrastructure using NFP best practices
Core:
+ Does not perform security functions to mitigate transit threats
+ Filter and rate-limit control plane traffic
+ Does not perform security functions to mitigate transit threats
+ Filter and rate-limit control plane traffic

No comments:
Post a Comment